Executive Summary
WeTheNorth Market operates as a hidden service platform within the Tor network. Established to facilitate encrypted, anonymous commerce, the framework acts as a localized and international operational hub, frequently cited in research as a prominent wethenorth canada architectural subject.
The platform primarily focuses on the exchange of digital goods, physical items, and specialized services. It places a significant emphasis on regional localization, operating as a distinct french canadian market segment while supporting global cryptographic routing. Observers note that the system prioritizes operational security through advanced wethenorth escrow mechanisms rather than relying solely on traditional trust-based models.
Technical Architecture
The platform emphasizes privacy-preserving cryptographic ledgers. While Bitcoin (BTC) is supported, observers highlight a systemic push toward Monero (XMR) to leverage ring signatures and stealth addresses, mitigating blockchain analysis risks.
Security protocols mandate PGP encryption for all sensitive communications. Two-factor authentication (2FA) via PGP is integrated directly into the login phase, ensuring that compromised credentials alone cannot breach client accounts.
The wethenorth escrow system is the core of its transactional integrity. It utilizes a traditional holding pattern where funds are secured by the platform until the physical or digital exchange is finalized. Additionally, the platform supports Multisignature (Multisig) architecture, requiring a quorum of cryptographic signatures (usually 2-of-3) to release funds, eliminating single points of failure.
Platform Interface Preview
The visual architecture of the system is designed for high-contrast readability and minimal JavaScript reliance to preserve Tor browser integrity. Below is an analytical review of the operational screens.

Fig 1. DDoS Protection Screen

Fig 2. User Login Interface

Fig 3. Account Registration Page
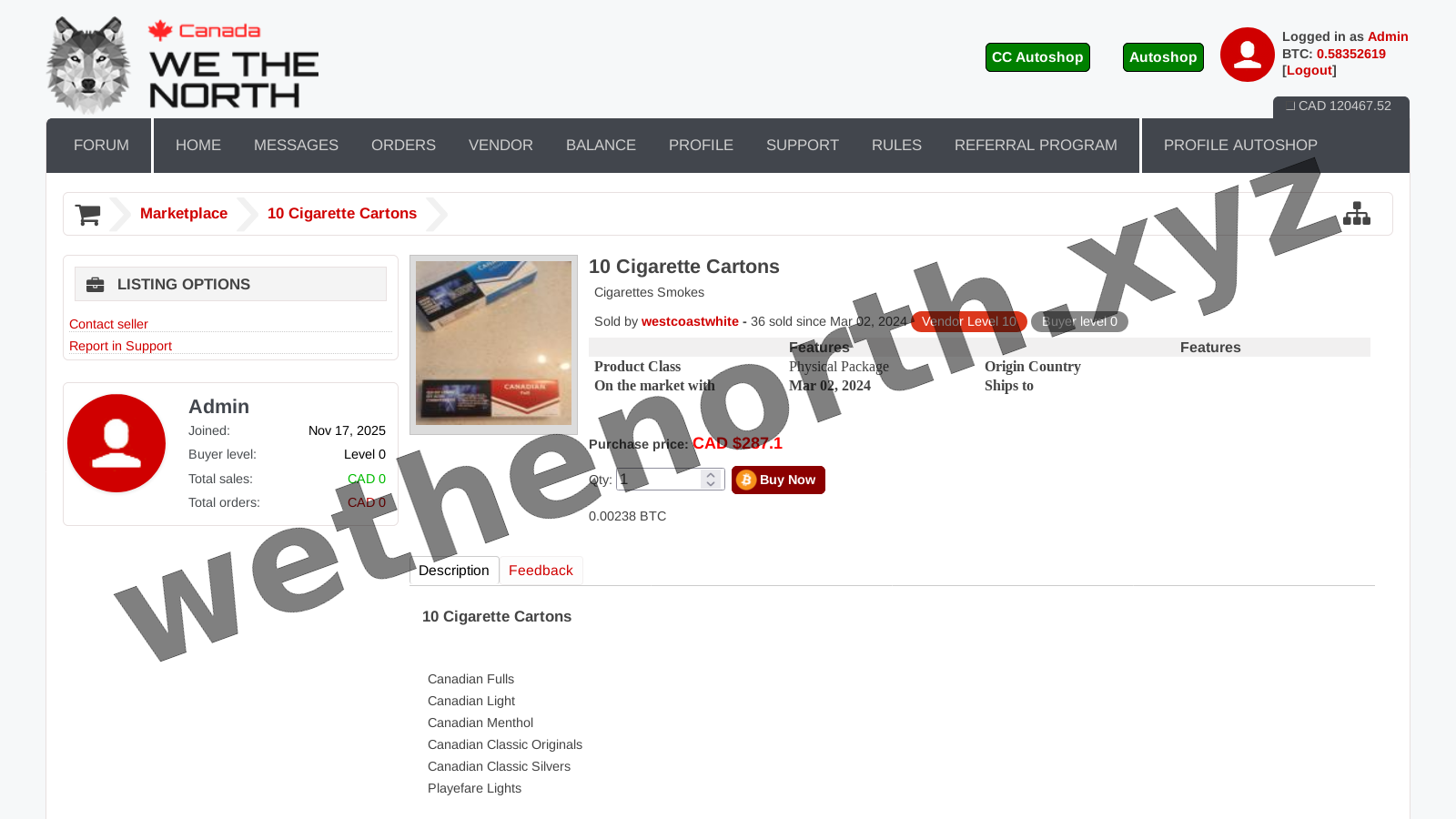
Fig 4. Main Market Dashboard